Browser security starts with visibility
Gain comprehensive insight into employee activity in every web browser to surface risk across your organization.
Eliminate the browser blind spot
Your employees spend up to 90% of their day in a web browser, accessing sensitive systems and data. That browser is a blind spot to traditional security tools.
Lack of visibility
Traditional security measures fail to capture browser-based employee activity, leaving a significant gap in enterprise defense.
Limited analysis
As threats become more and more browser and application based, security teams are unable to analyze in-tab interactions.
Ineffective response
Elevate your security posture
with comprehensive browser security
How does Keep Aware address browser visibility?
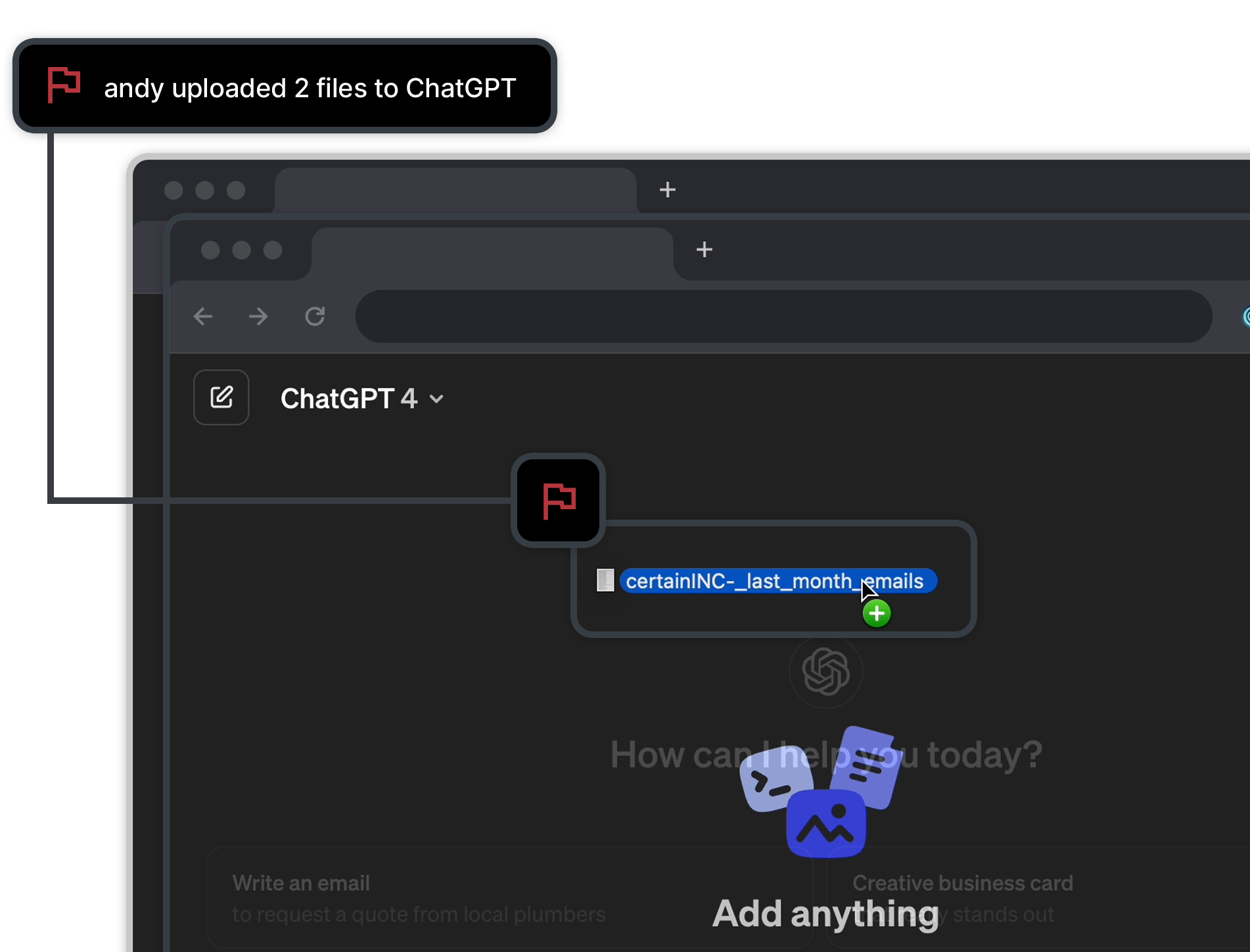
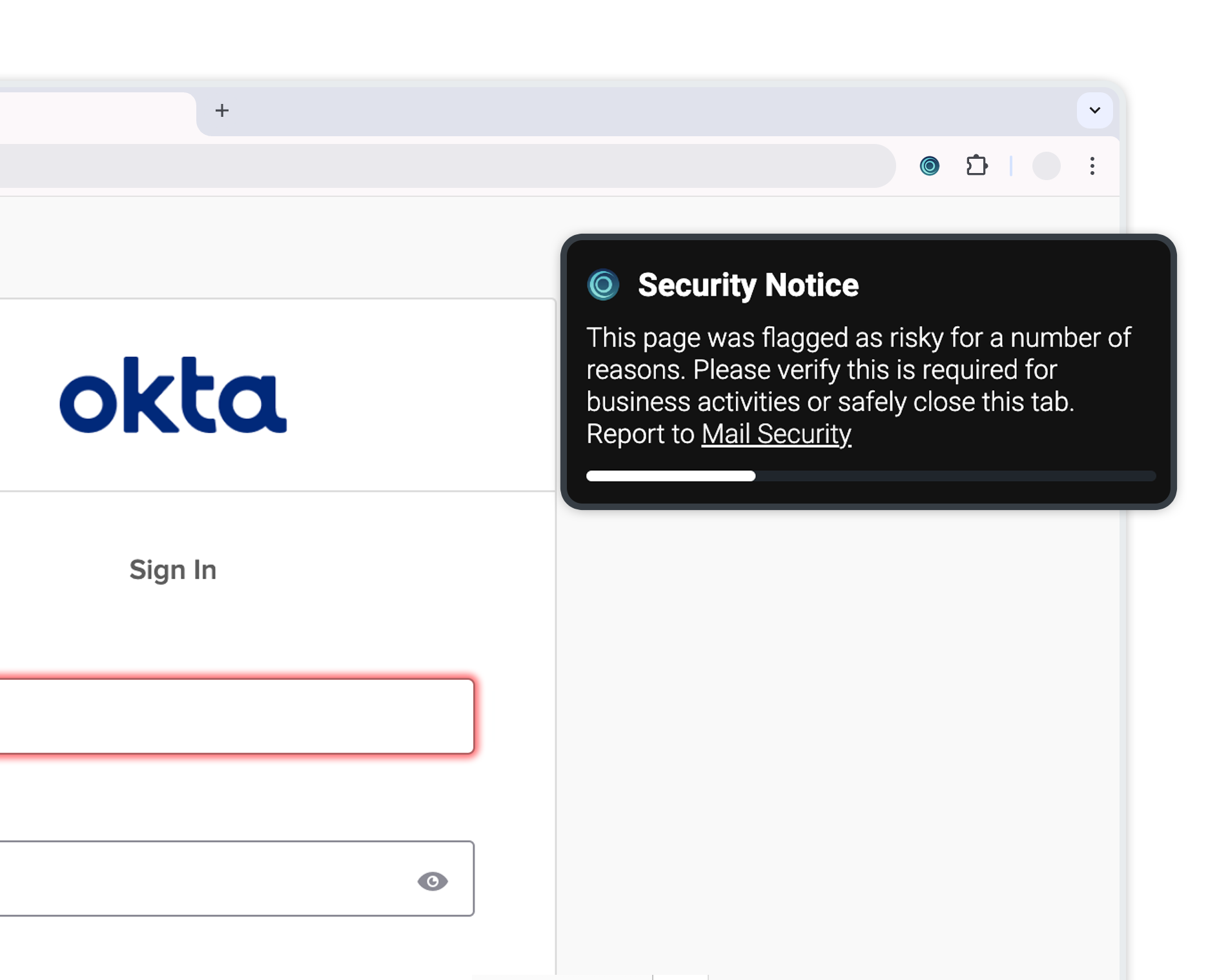
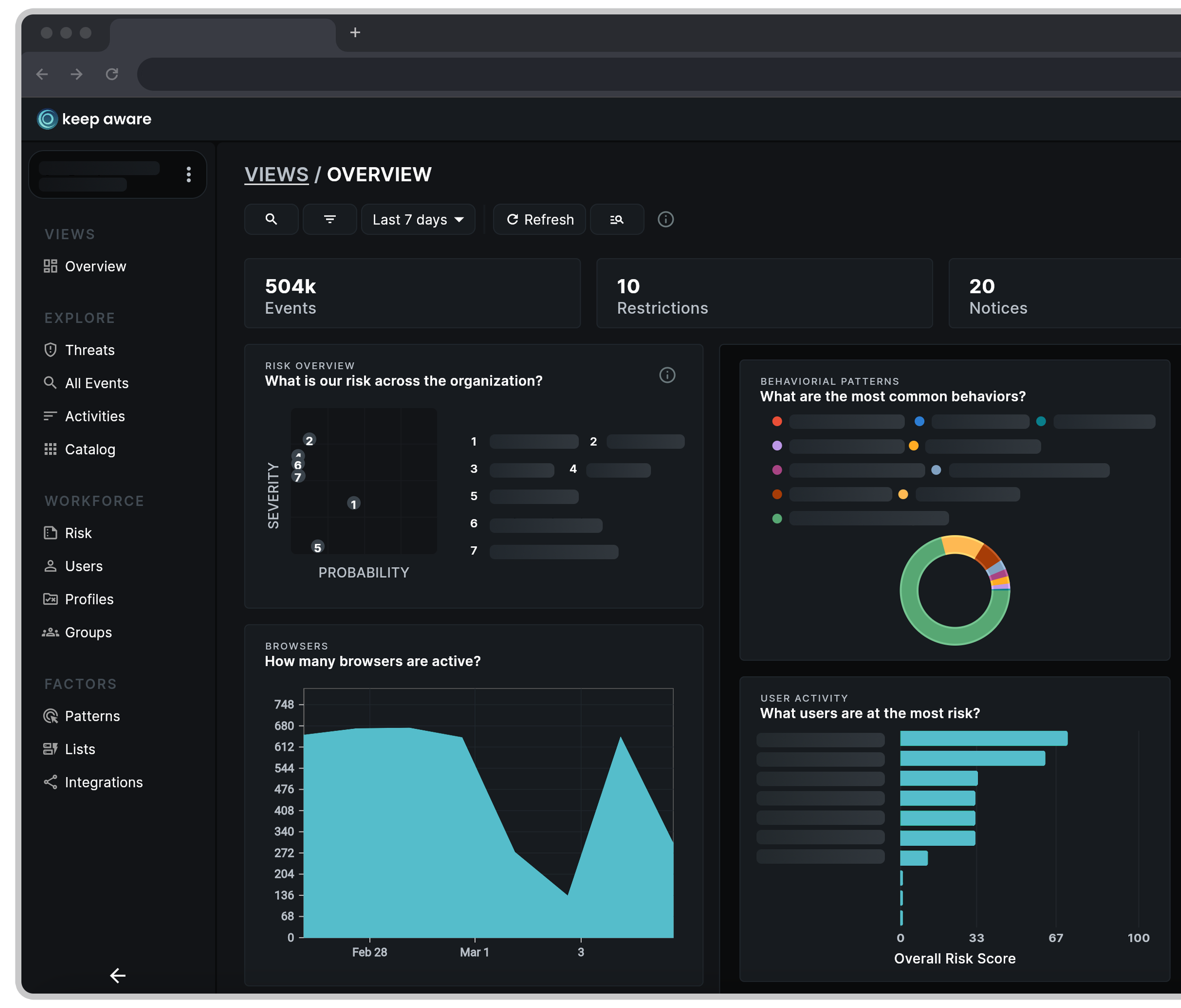
Real-time monitoring and alerting
Instantly identify and respond to any risky activity across all standard web browsers. Gain comprehensive insight into unknown and known risks, and swiftly address threats to your employees.
In-depth behavior analytics
Uncover behavior patterns, unusual activity, and threats in real-time, ensuring continuous employee-facing protection for your organization.
Risk scoring and prioritization
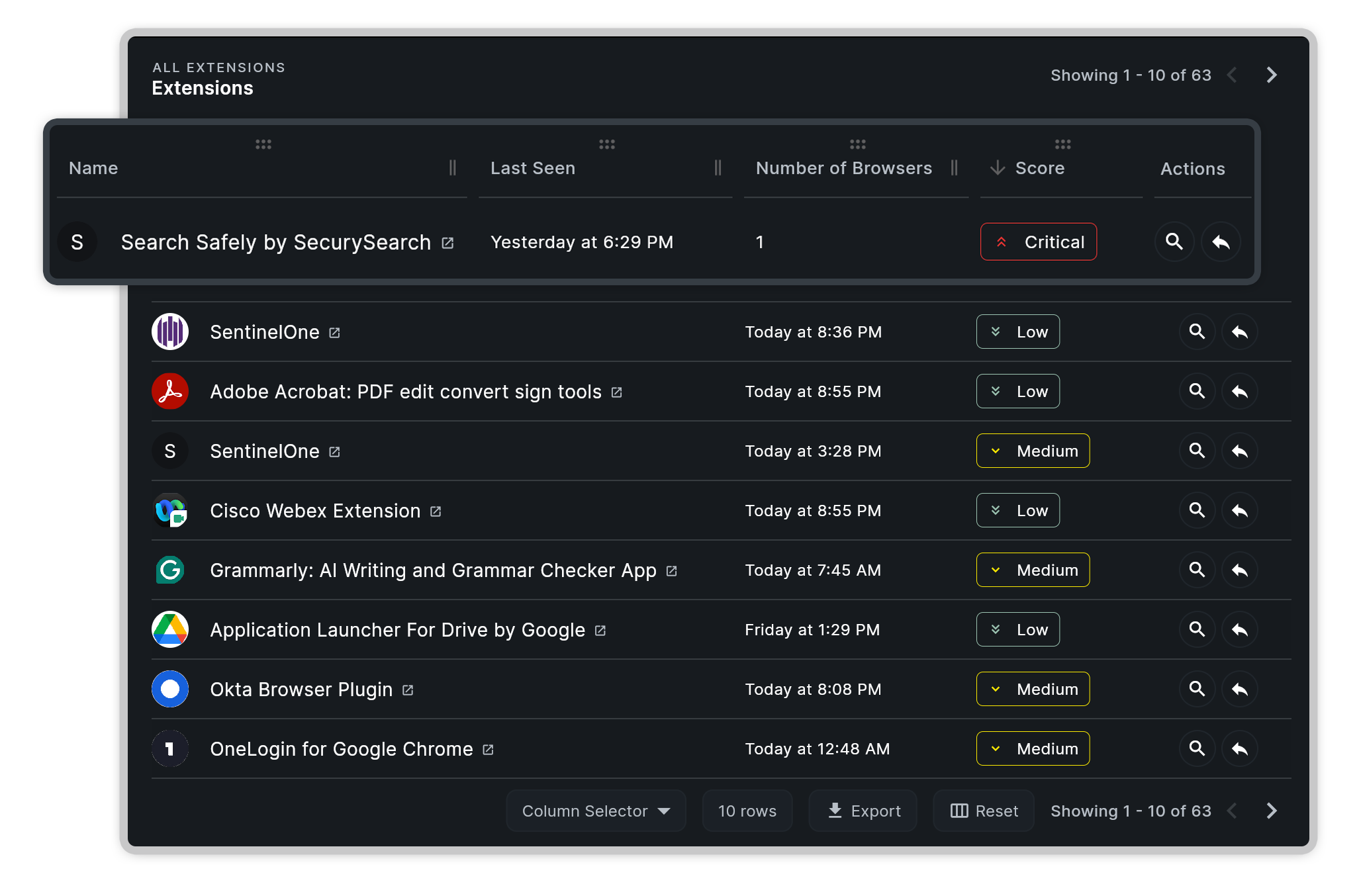
Immediately identify risk and focus on the most pressing browser-based activities. Streamline security operations for employee-facing threats such as phishing, social engineering, and malicious browser extensions.
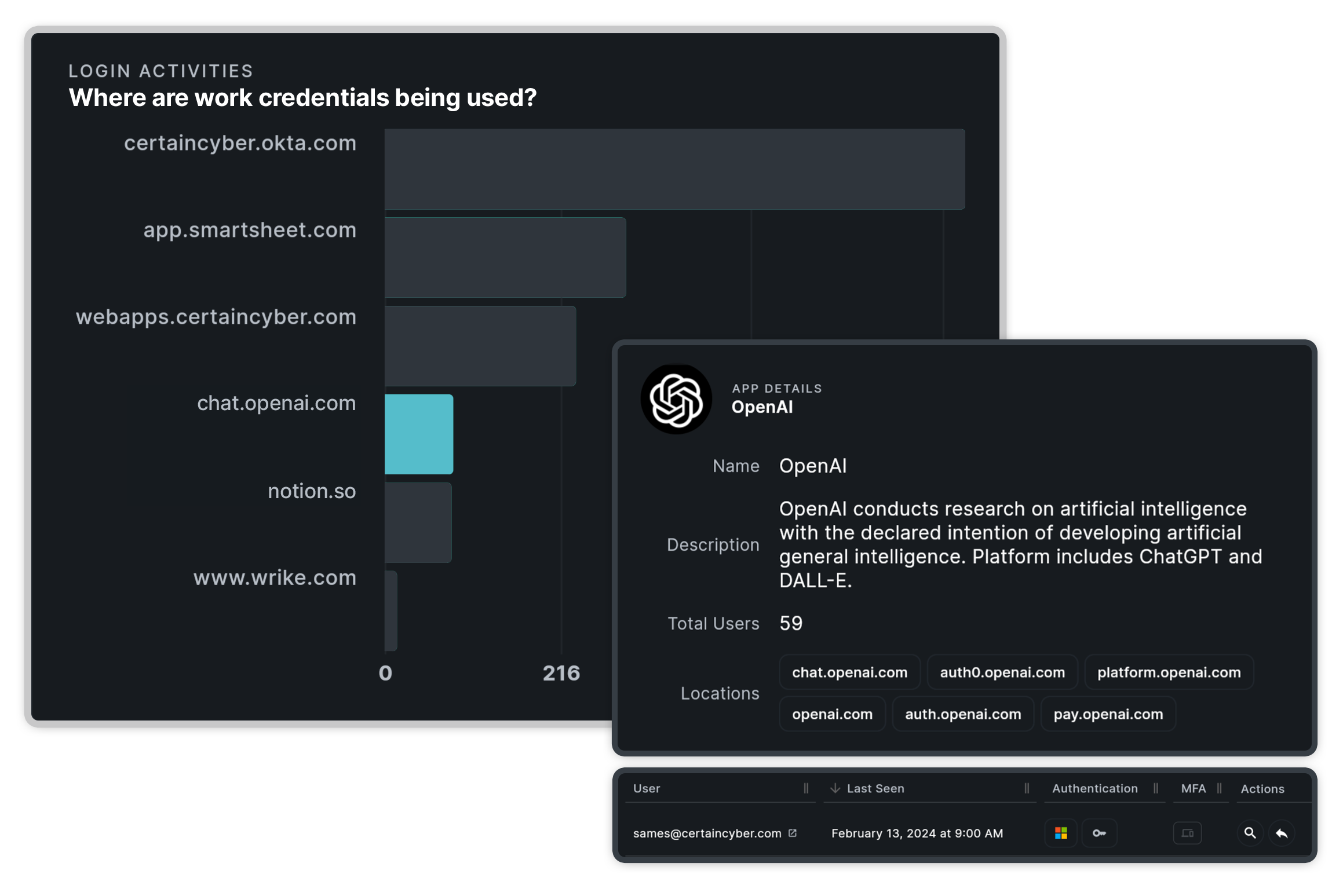
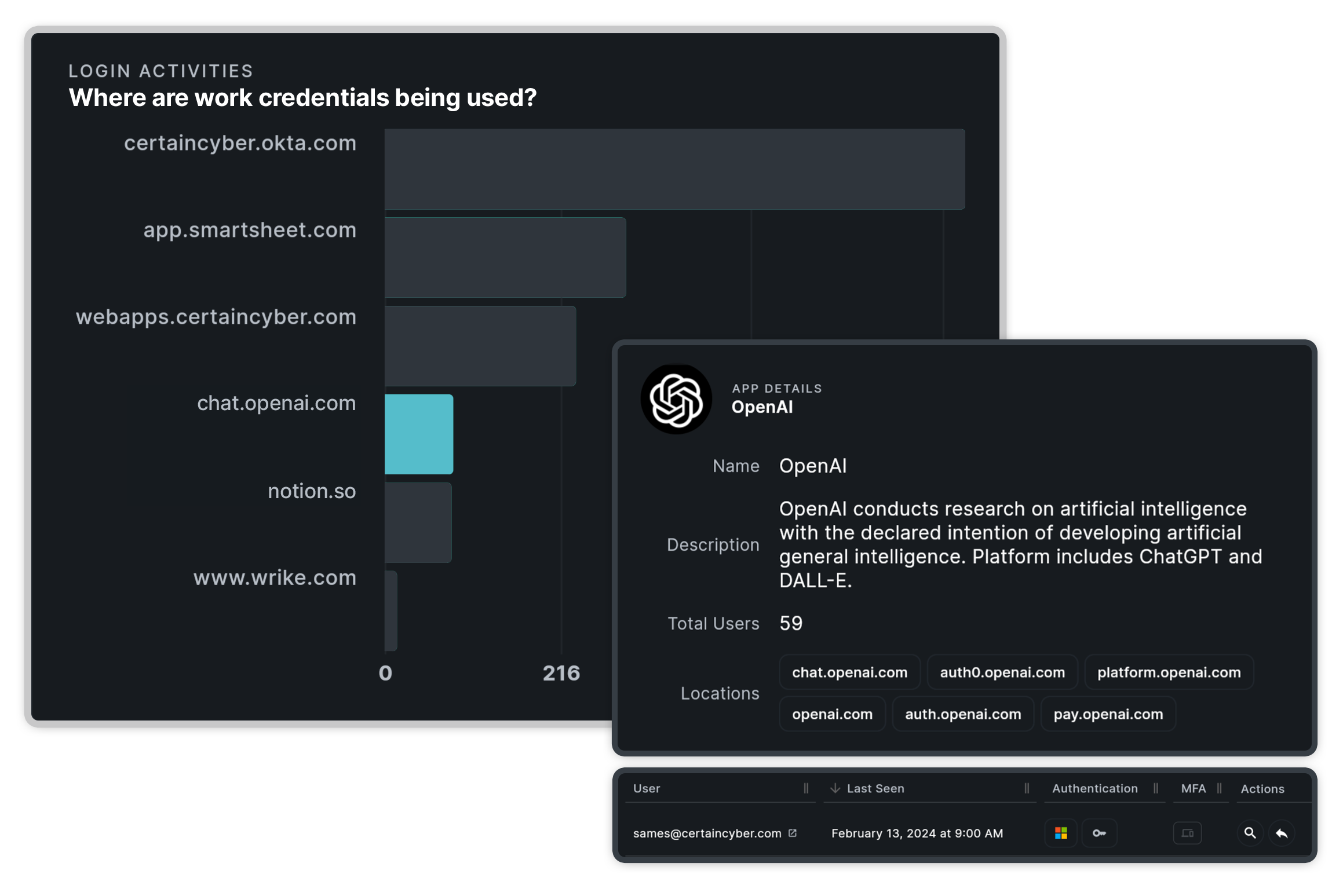
Reporting on high risk browser activity
Automate reporting for comprehensive insight and transparency into high risk employees and activities. Track file transfers, SaaS sprawl, shadow IT, and work credential usage with crystal-clear visibility.
Visibility is just one requirement for a secure browser
is the next important security initiative
Protect your employees where they work — the web browser
Discover how to transform any browser from a blind spot to a pivotal security control. Keep Aware turns everyday browsing into a proactive security experience, safeguarding against emerging threats in real time.
Related Resources
- Threats
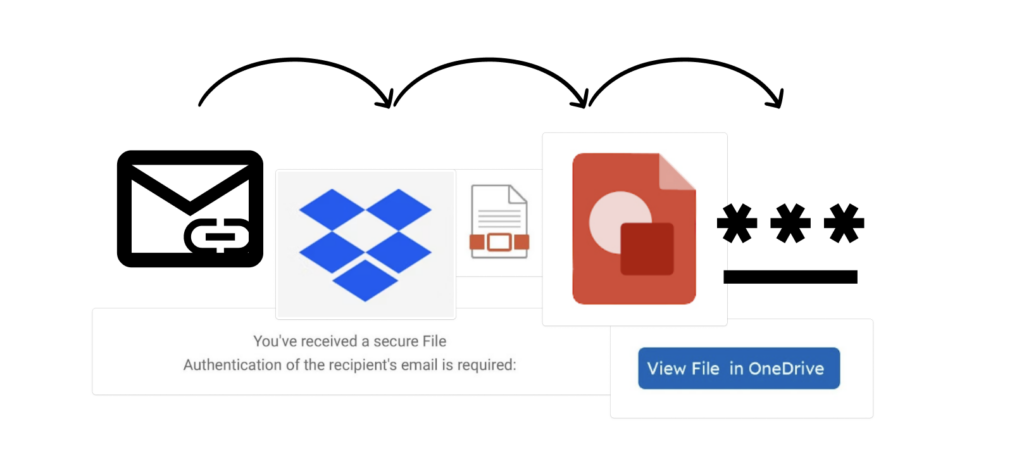
A Link, Click, and a Phish Away! Using Legitimate Domains for a Multi-Step Phishing Attack

- Threats
“Looking” for Documents? .. “Look” No Further: A New Trend in Abusing Google Looker Studio for Phishing
- Threats
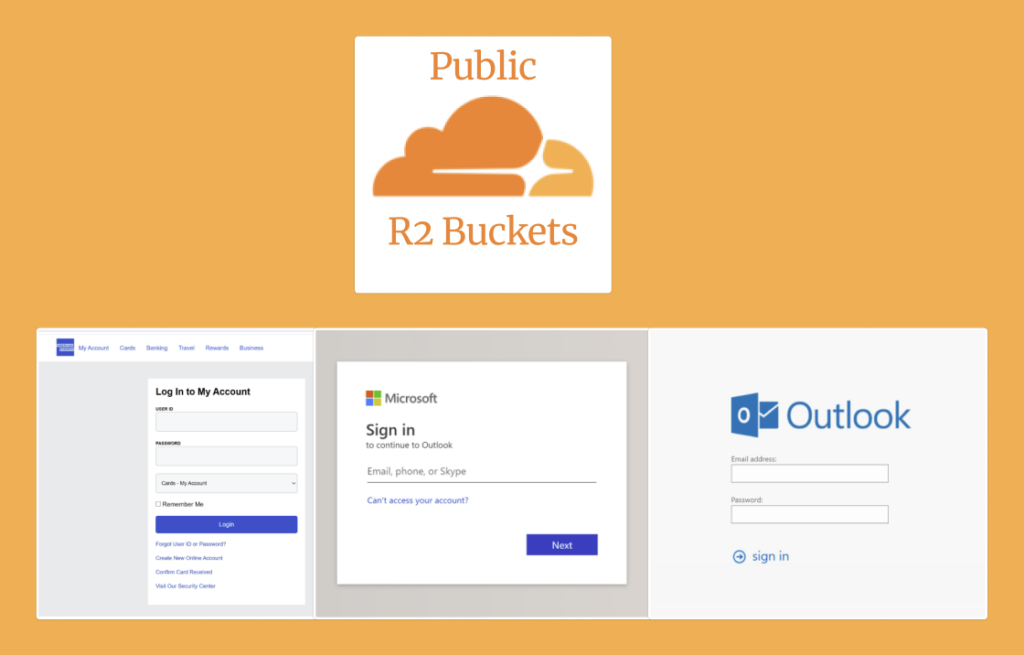
Cloudflare R2, Public Buckets and a Phishing Binge: An Analysis of Today’s Threat Landscape
- Threats
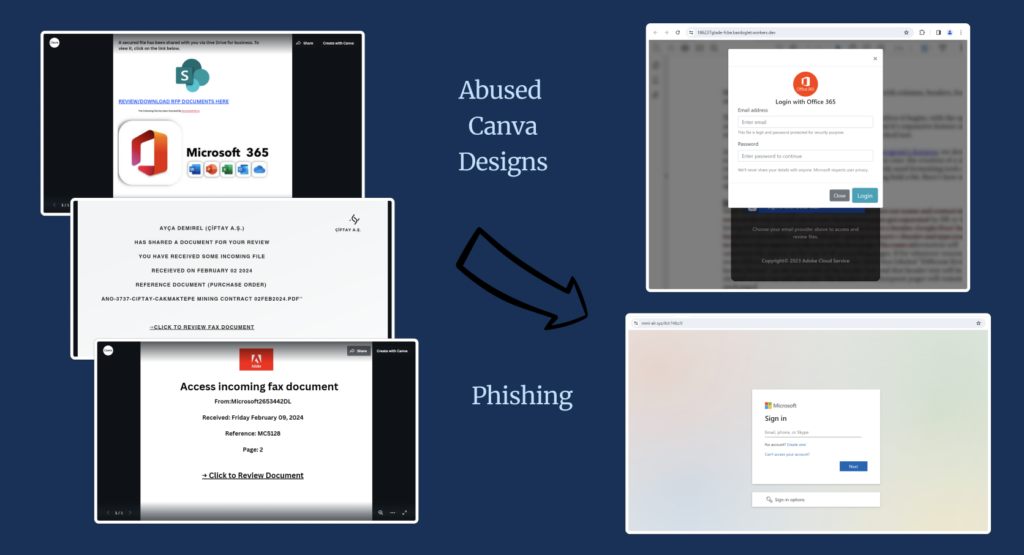
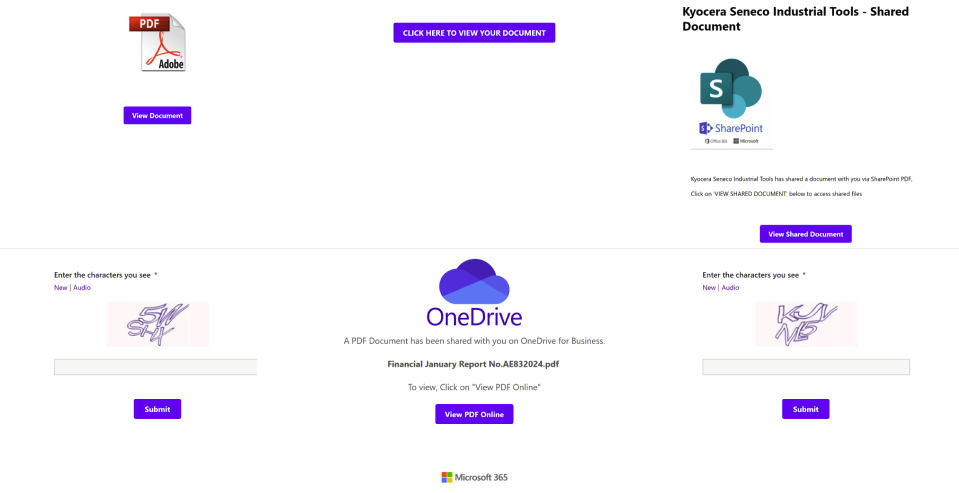
Clicking Links, From Canva Design to Phishing Site: An Analysis of Today’s Threat Landscape
- Threats
