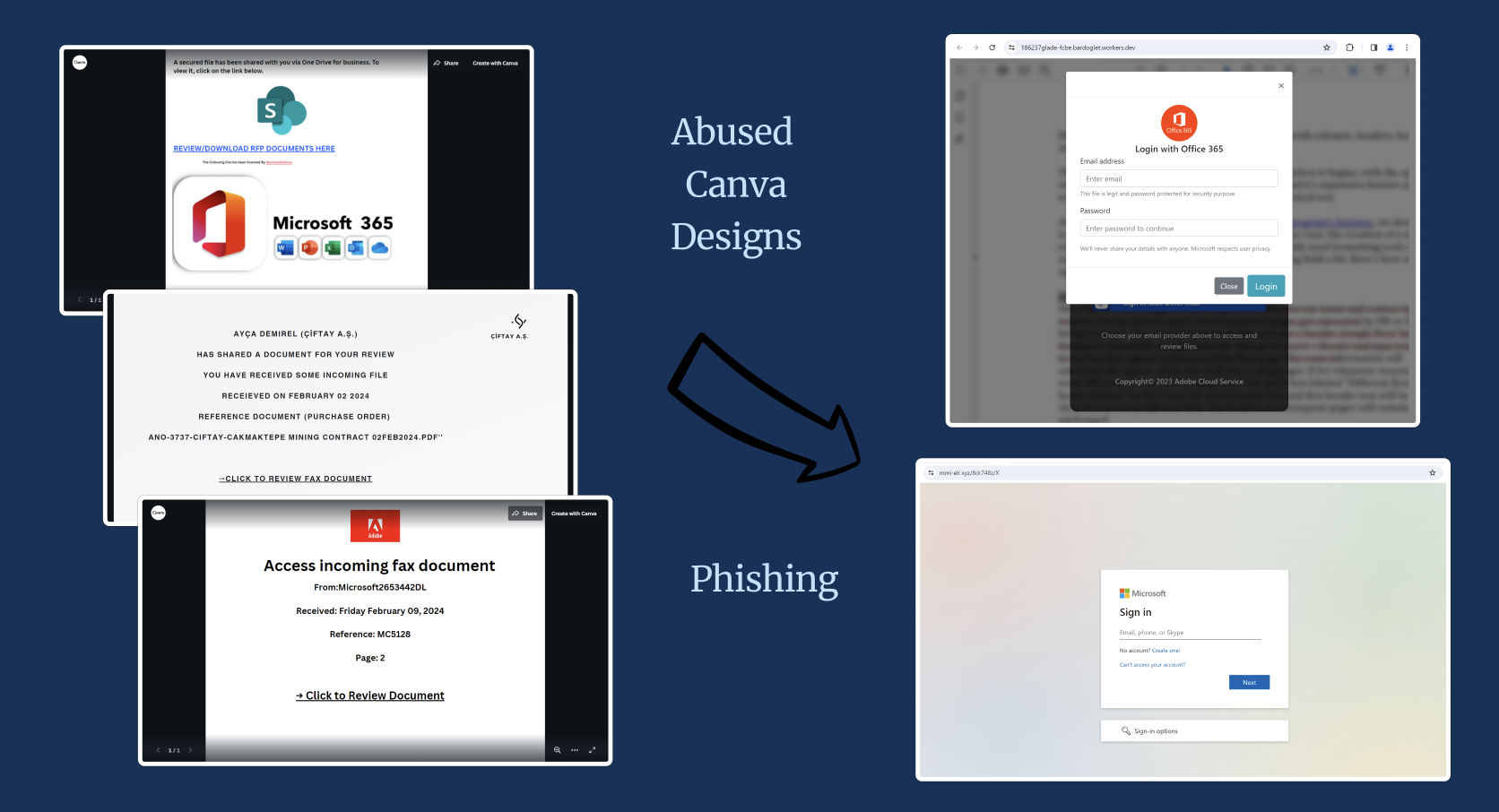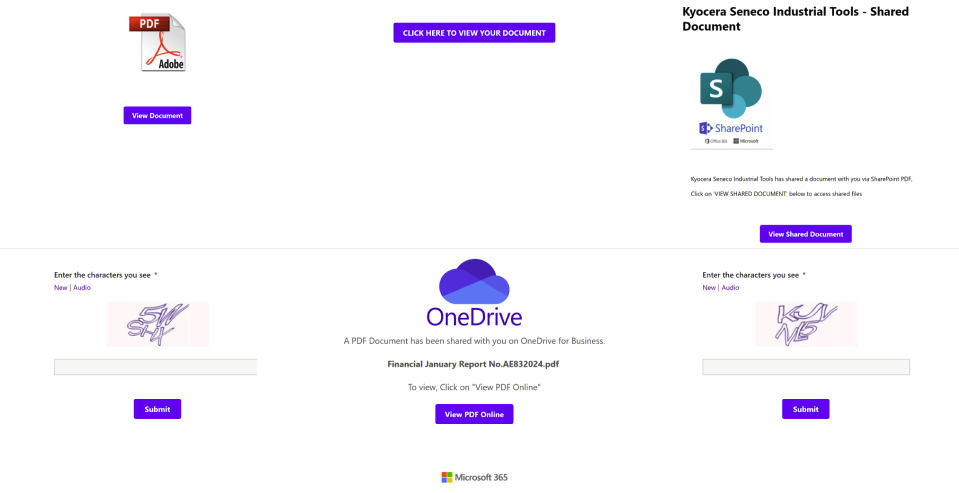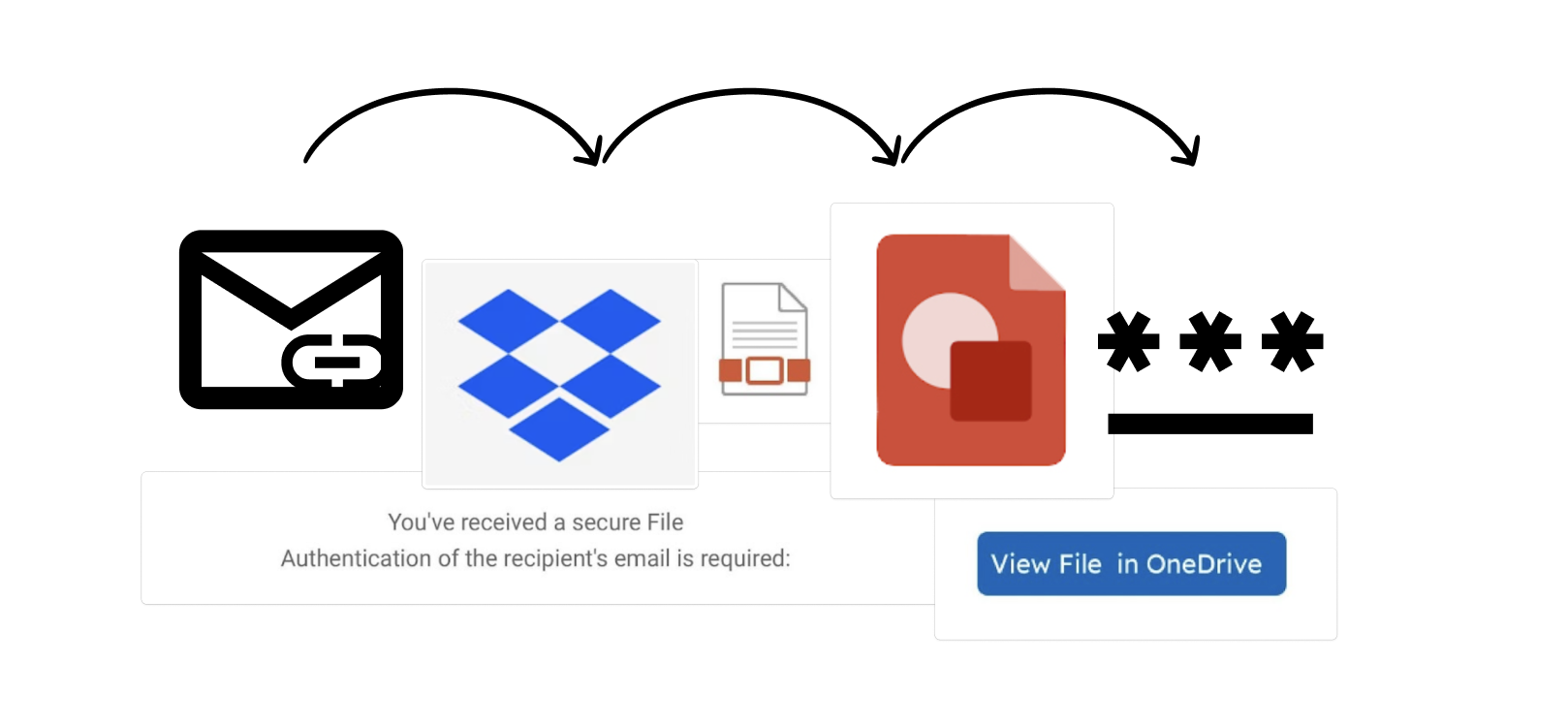
A Link, Click, and a Phish Away! Using Legitimate Domains for a Multi-Step Phishing Attack
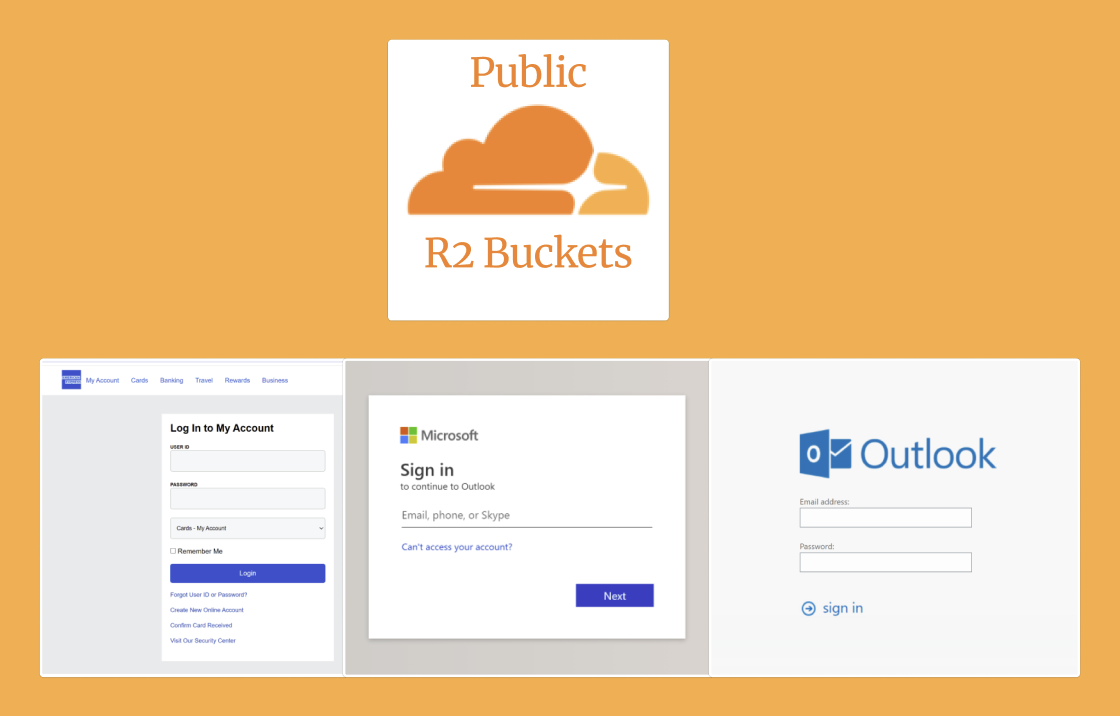
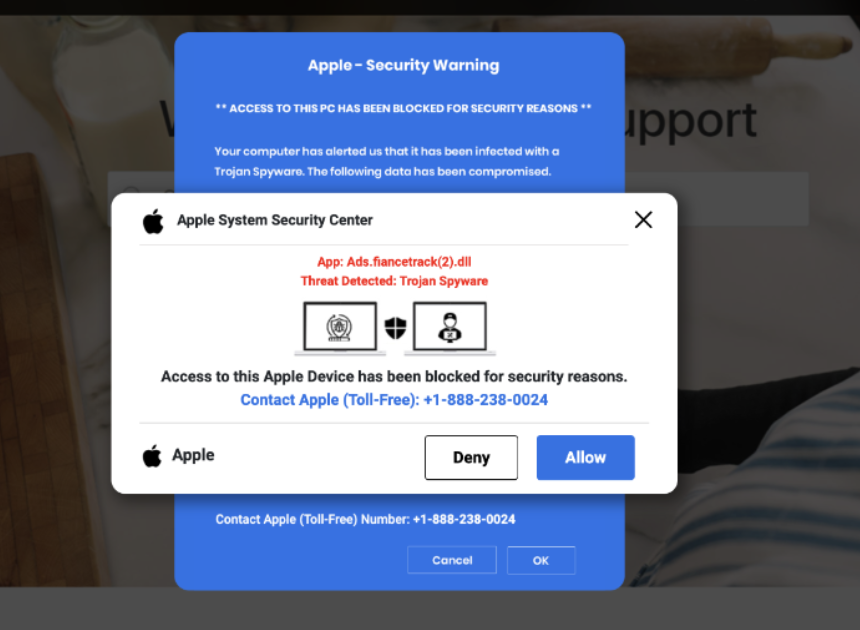
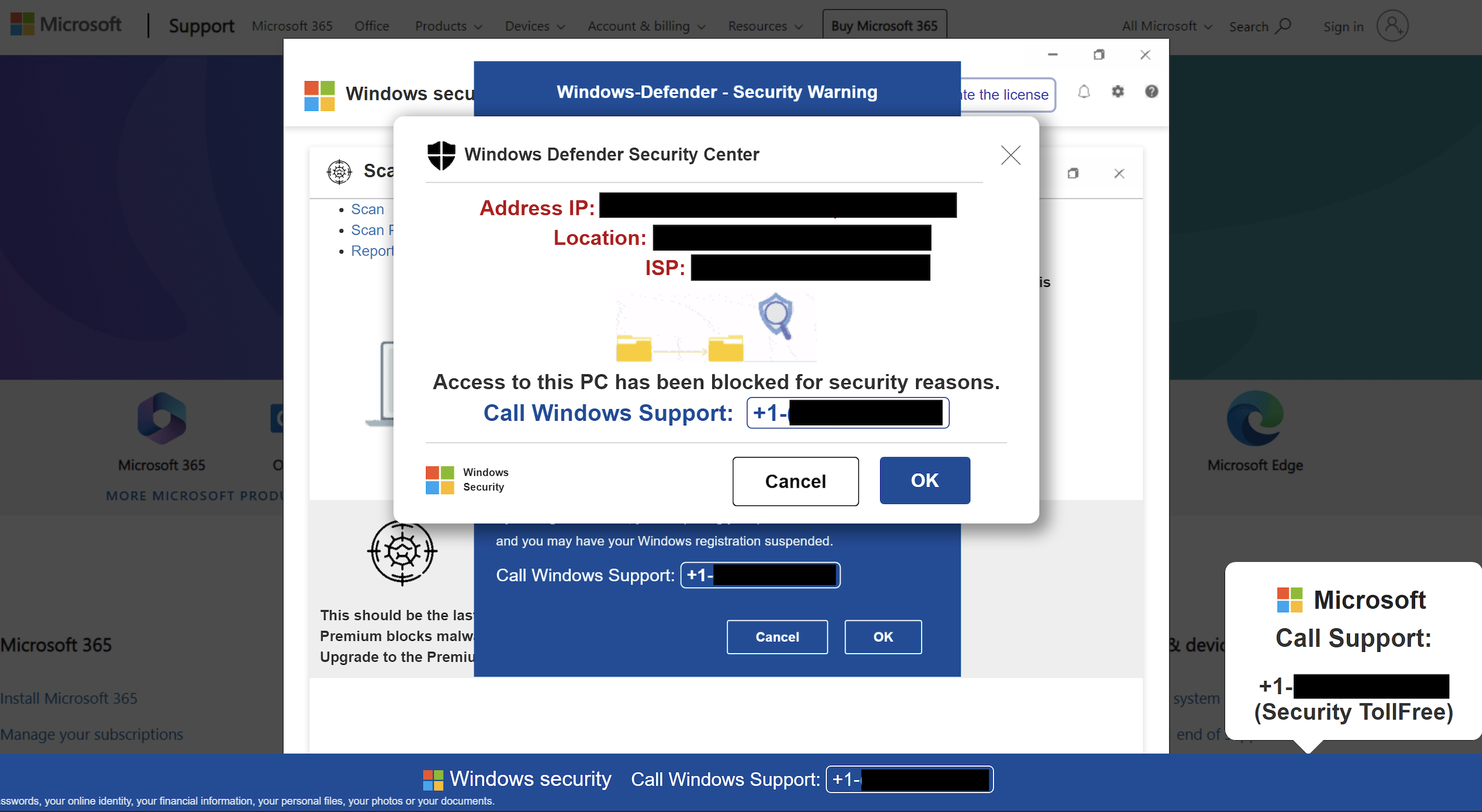
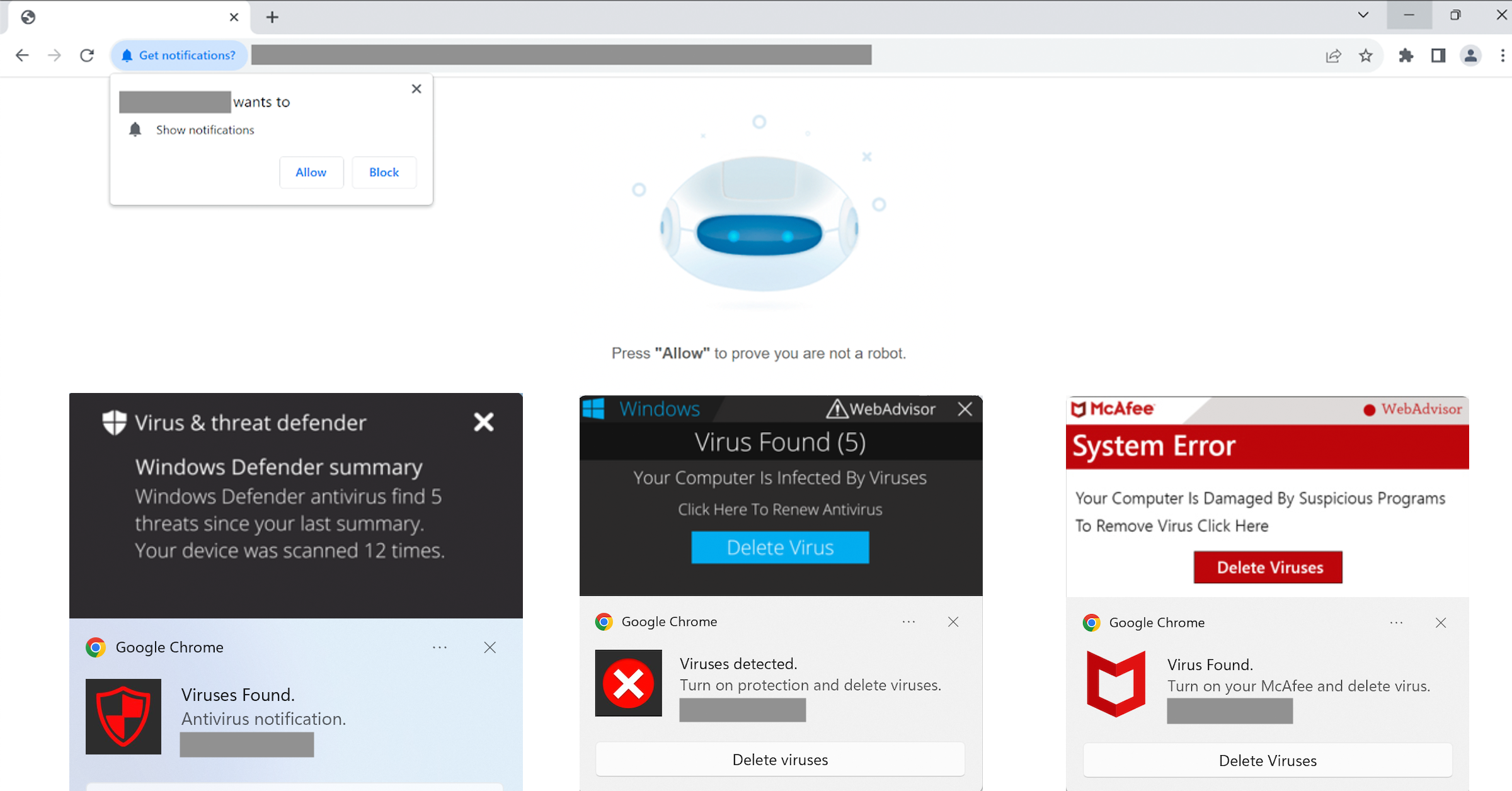
Key points: Overview Keep Aware has observed phishing attacks that use legitimate domains to host links that eventually lead to a credential stealing web page.