Extend granular policy to the browser
Standardize browser security controls and deploy employee-level safeguards across every web browser.
Existing security controls don't govern what happens within the browser
Lack of granular
controls
Most legacy security solutions cannot adequately analyze what happens within the browser.
Inconsistent browser policies
Security controls for employees vary across Chrome, Edge, Firefox, and other browsers, making policy creation cumbersome and inconsistent.
Ineffective policy communication
Centrally manage all browser governance
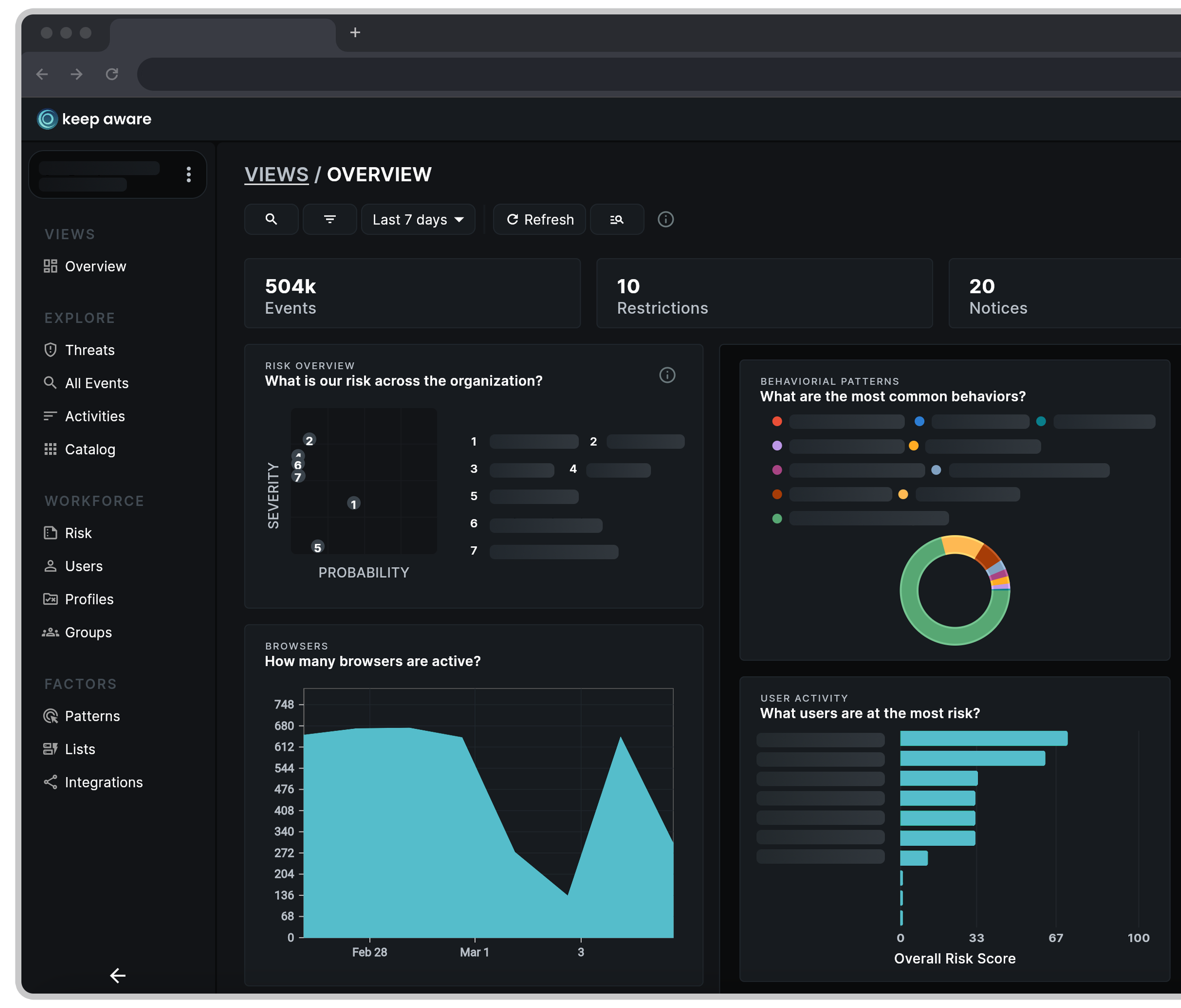
How does Keep Aware centralize controls and policies across all browsers?
Comprehensive policy management
Govern the extensions, workspaces, and SaaS applications used across Chrome, Edge, Firefox and other industry-standard web browsers.
Sensitive data leakage controls
Prevent sensitive and risky copy/paste, prompts, file sharing, and credential activity without tunneling your traffic to a third-party.
Real-time policy enforcement
Prevent access to unauthorized applications within the browser and block suspicious logins, file sharing, and data entry at the point of click.
Continuous activity and risk monitoring
Governance is just one requirement for a secure browser
is the next important security initiative
Protect your employees where they work — the web browser
Discover how to transform any browser from a blind spot to a pivotal security control. Keep Aware turns everyday browsing into a proactive security experience, safeguarding against emerging threats in real time.
Related Resources
- Threats
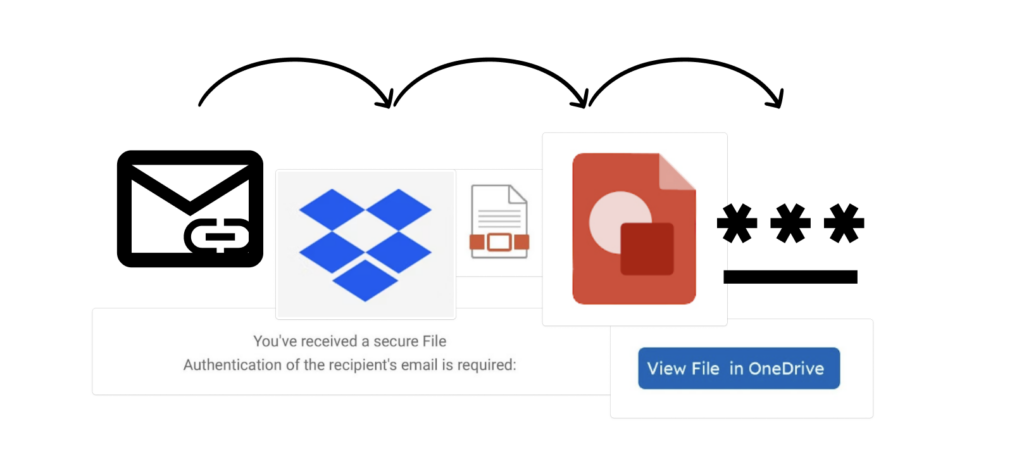
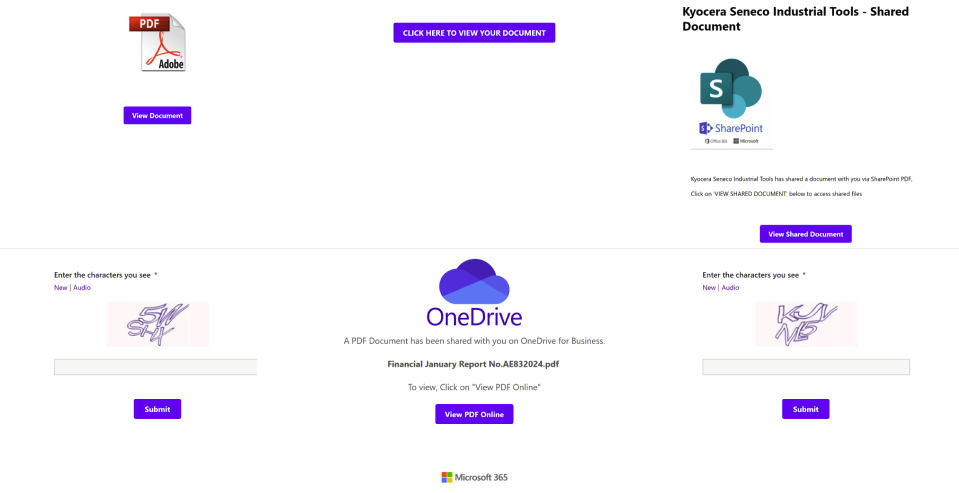
A Link, Click, and a Phish Away! Using Legitimate Domains for a Multi-Step Phishing Attack

- Threats
“Looking” for Documents? .. “Look” No Further: A New Trend in Abusing Google Looker Studio for Phishing
- Threats
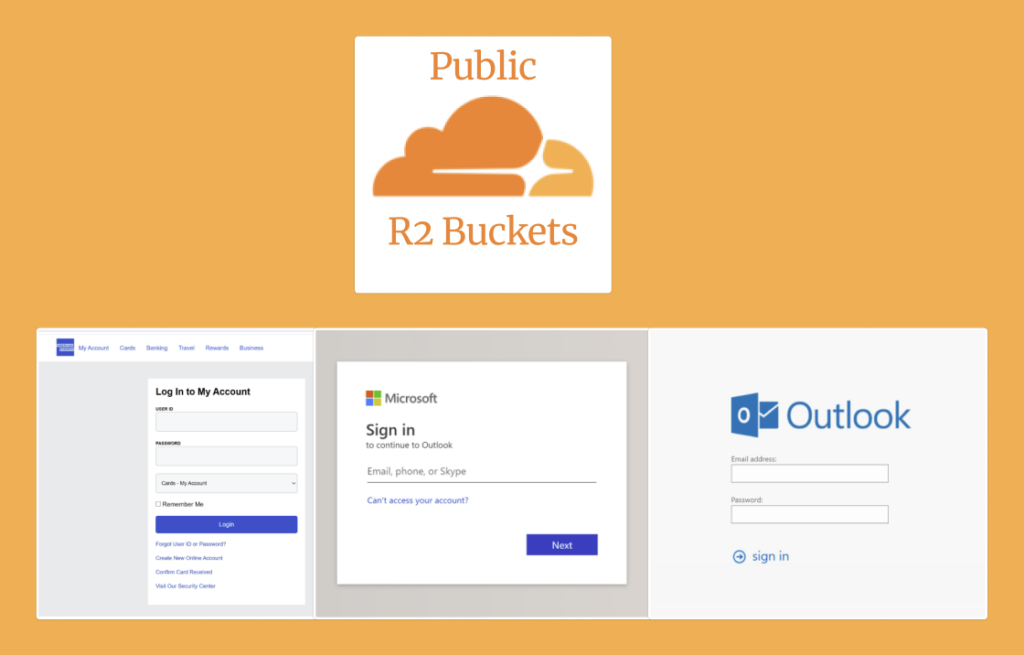
Cloudflare R2, Public Buckets and a Phishing Binge: An Analysis of Today’s Threat Landscape
- Threats
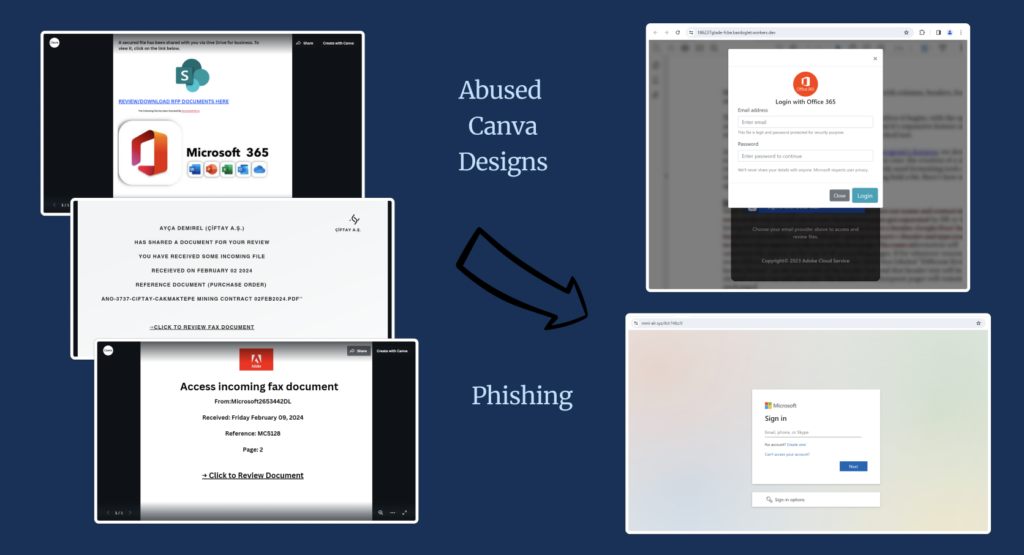
Clicking Links, From Canva Design to Phishing Site: An Analysis of Today’s Threat Landscape
- Threats

