
In our State of Browser Security Report, our team noted several types of attacks that emerged (or rapidly matured) in 2025 and bypass traditional controls by operating within browser activity. These active threats are highly effective and difficult to detect with traditional security tooling alone.
Three in particular stand out: ClickFix, ConsentFix, and what we call “sleeper” extensions.
1. ClickFix: When a Copy-Paste Becomes a Device Compromise
ClickFix attacks weaponize one of the most trusted user actions in the browser: copy and paste.
A malicious webpage silently injects attacker-controlled commands into the user’s clipboard. The user is then socially engineered, often through fake error messages or verification instructions, to paste the content into a terminal, PowerShell, or command prompt. The user unknowingly compromises the device, deploying remote access trojans (RATs), installing data stealers, or otherwise providing the attacker persistence on the host machine.
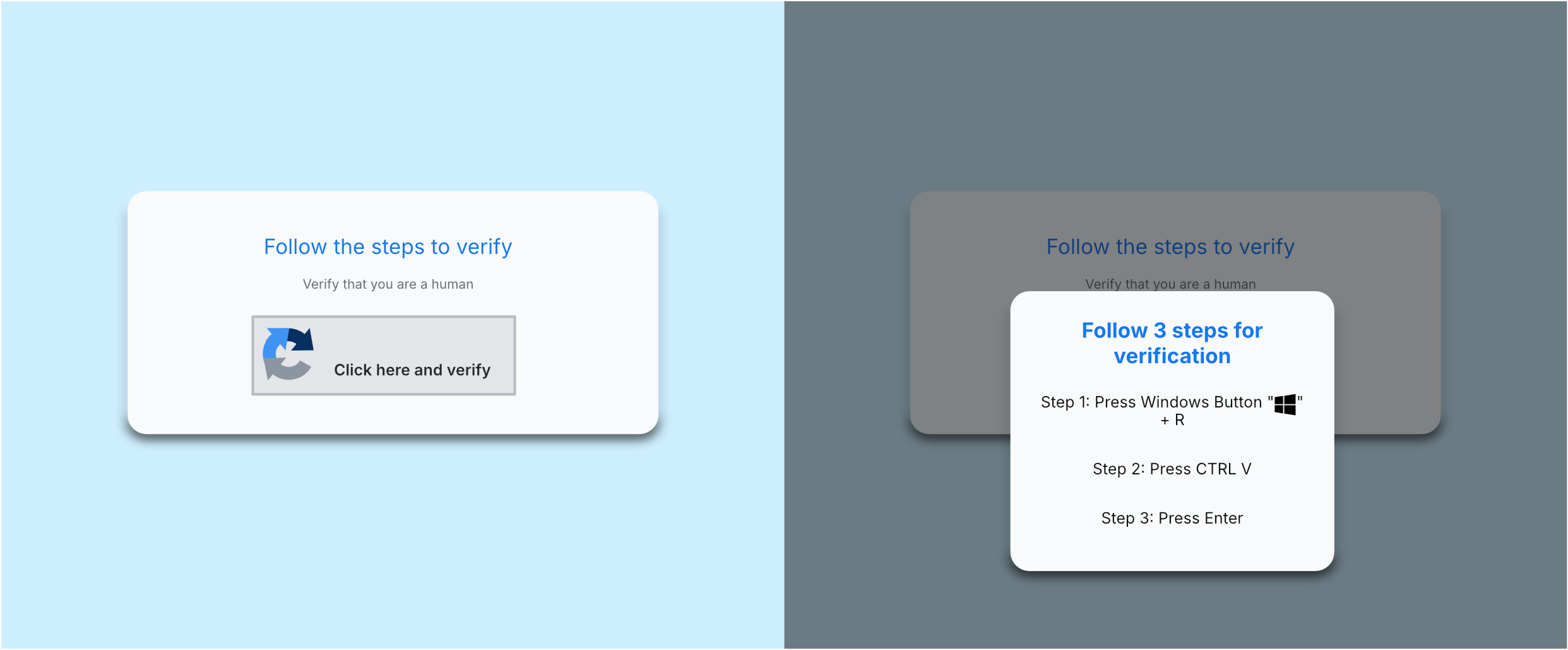
ClickFix attacks don’t require exploits or unpatched vulnerabilities. They abuse legitimate browser functionality (populating clipboard contents) and manipulate user behavior. This means they bypass traditional prevention controls and and rely on getting the user to execute malicious actions themselves, leaving endpoint tools as the first and last opportunity to detect malicious activity.
Users encounter these attacks through SEO-poisoned search engine results, compromised websites, and increasingly, GenAI or LLM-generated responses that give malicious instructions or links. These delivery channels are often trusted and high-volume, making ClickFix both highly scalable for attackers and extremely difficult for security teams to stop ahead of time without visibility into user actions in the browser.
2. ConsentFix: OAuth Abuse Without Credentials
ConsentFix leverages something security teams inherently trust: OAuth flows.
Instead of stealing credentials, attackers trick users into completing a legitimate authorization flow, then pasting the resulting authorization code into an attacker-controlled site. Without providing credentials or triggering MFA prompts, the attacker can then access the victim’s cloud account.
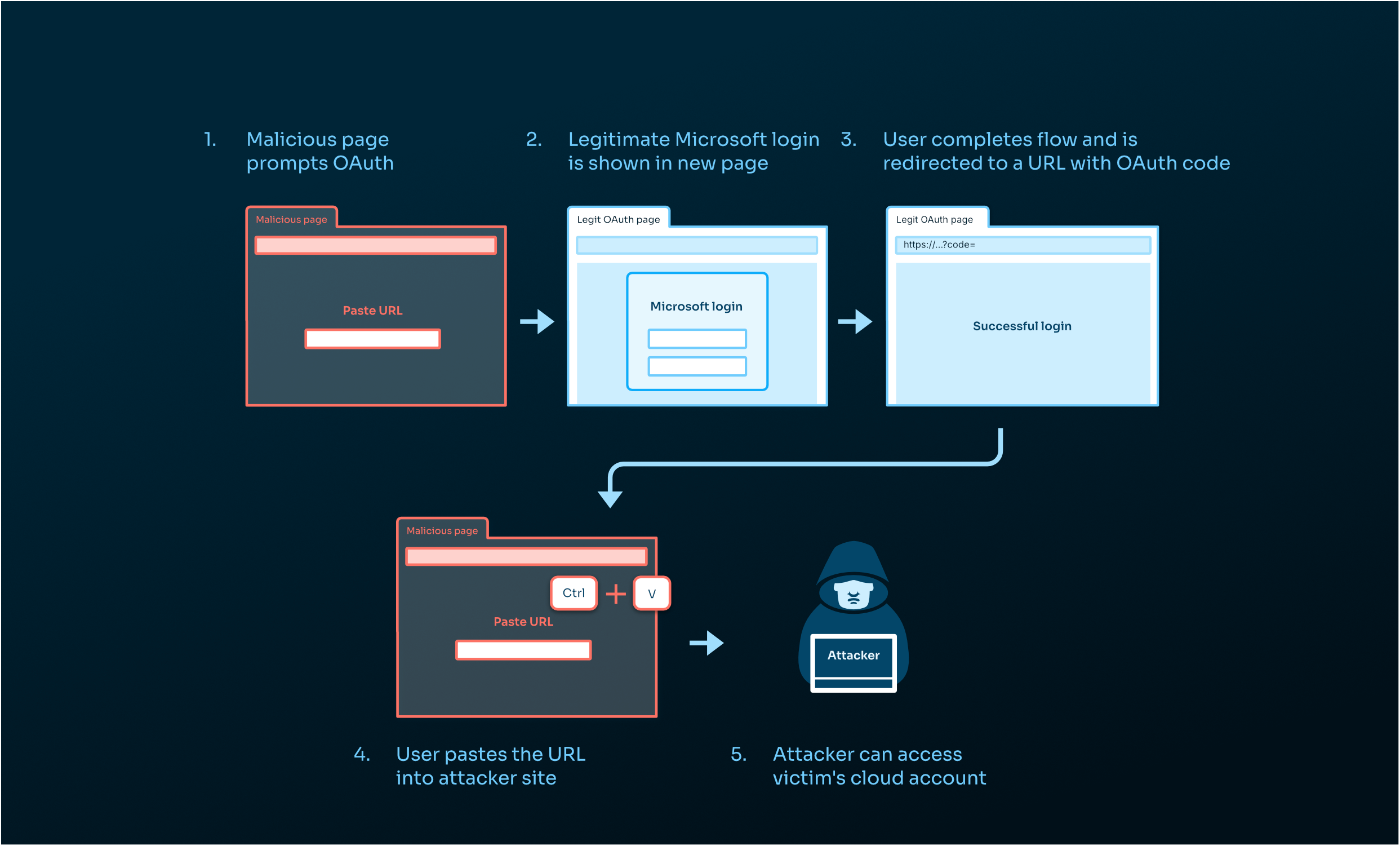
ConsentFix relies on trusted identity infrastructure and tricking users into providing a sensitive code via the browser, enabling attackers to evade detection across network and endpoint layers. These attacks also evade identity controls because an attacker creates neither anomalous login events nor MFA prompts.
3. “Sleeper” Extensions: Persistent Access Executing in Plain Sight
Malware sleeper extensions exploit one of the most permissive components of a browser: already-installed extensions.
Sleeper extensions appear legitimate when installed, providing real functionality to a user’s experience. But over time, they receive updates or remote configuration changes that activate malicious behavior.
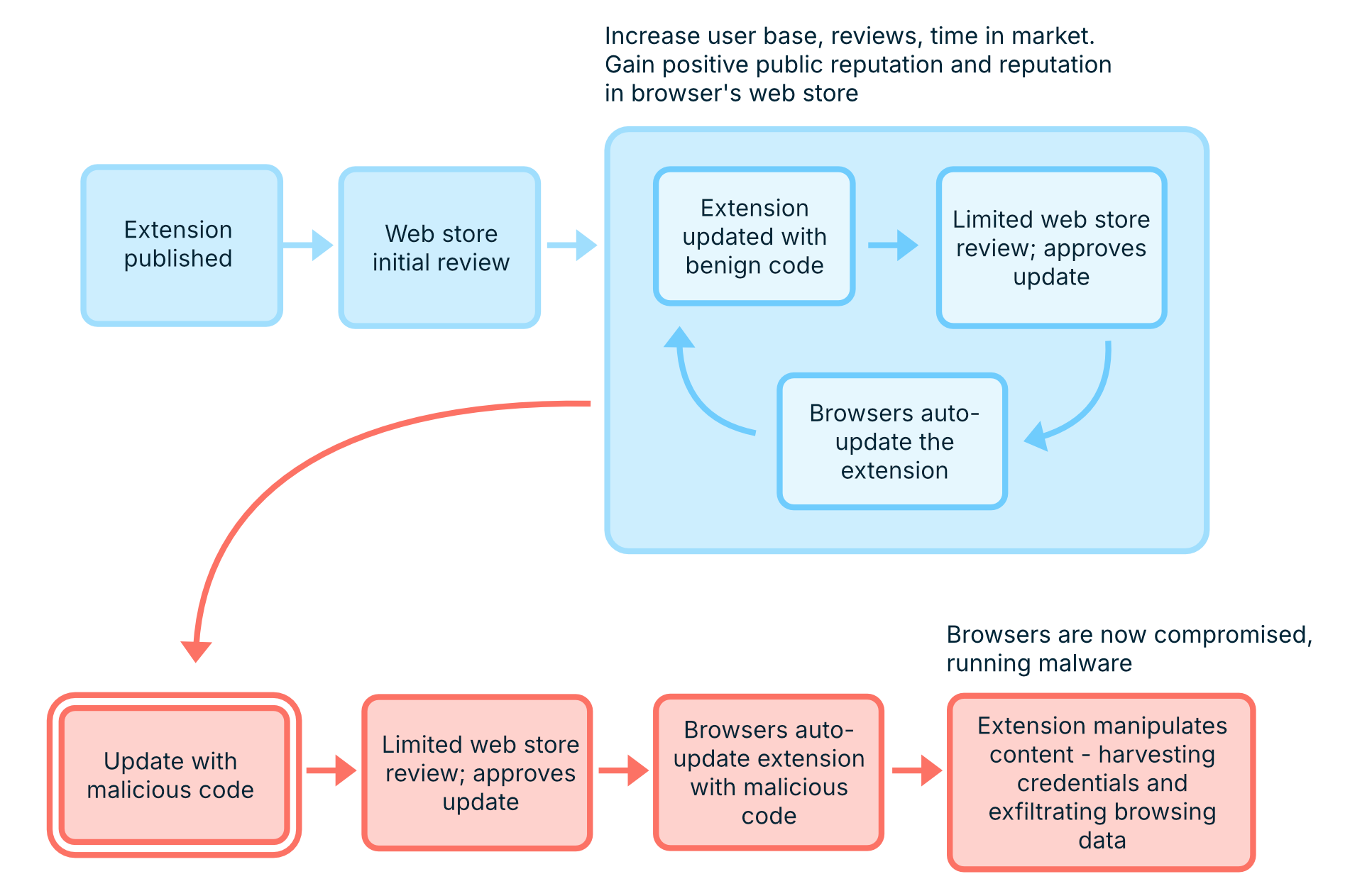
When a user installs an extension, security tools might perform a point-in-time analysis of the new add-on. But rarely do add-ons get checked a second or third time. So sleeper extensions, appearing legitimate at install, bypass traditional security controls.
This attack dupes tools and users into a false sense of security, believing there is a benign add-on installed, then abusing the lack of ongoing security validation after initial approval to spy on user activity, exfiltrate sensitive data, and harvest credentials sent over the browser interface.
The Big Shift: The Browser Is the Attack Surface
These attacks underscore a common pattern: attackers don’t break the browser, they abuse it.
By using normal copy-paste activity, legitimate authorization workflows, and reputationally “benign” extensions, these newer browser-based attacks can easily bypass traditional controls, including email security, secure web gateways, endpoint detections, identity protections, and single point-in-time analyses.
The interface we each use every day is the same application that attackers are abusing because traditional controls leave it undersecured.
What This Means for Security Teams
If you’re responsible for securing a modern workforce, you need visibility and control inside the browser—not just around it.
That means:
- Monitoring user-driven actions (not just downloads and URLs)
- Inspecting OAuth flows and authorization behavior
- Continuously evaluating extension risk post-install
- Correlating activity across users with your organization’s unique context
Without that, these attacks slip through and operate undetected.
If you want to dive deeper into the risks evolving in today’s modern workforce and what security teams are doing about them, check out the full State of Browser Security Report 2026.


%20copy.jpg)
.png)