
Over the past year, our research and BDR investigations across customers have revealed a consistent pattern: Modern phishing and browser-based attacks are engineered specifically to evade automated analysis, reputation systems, traditional perimeter controls, and out-of-band (OOB) analysis.
Most traditional controls evaluate URLs and domain homepages in isolation. But attackers now design campaigns that only become malicious after specific in-browser interactions or other conditions are met.
Below are several evasive procedures we’re repeatedly observing.
5 Evasive Attacker Procedures We Repeatedly Observe
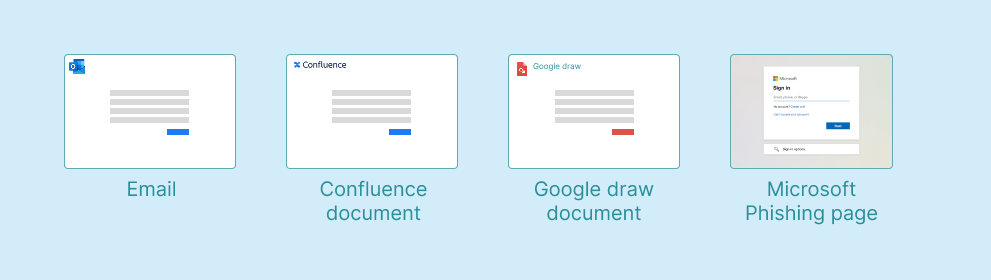
1. Chained Attack Sequences That Conceal Intent
Rather than exposing malicious content immediately, many campaigns now unfold across multiple controlled steps:
- Redirect chains across different domains
- Email address validation before progressing
- Access codes or staged landing pages
- Conditional logic triggered by browser attributes
- CAPTCHA gates
Only after a user completes certain actions—or if the user’s browser has certain characteristics—does the final phishing or malicious page appear.
To early security controls, the early stages often look benign.
To automated tools, the domains used appear benign.
To the victim, the final stage is fully weaponized.
These sequences hide the true malicious destination and content from non-browser tools, evading traditional security tools and enabling attack campaigns to be more successful and longer-lived.
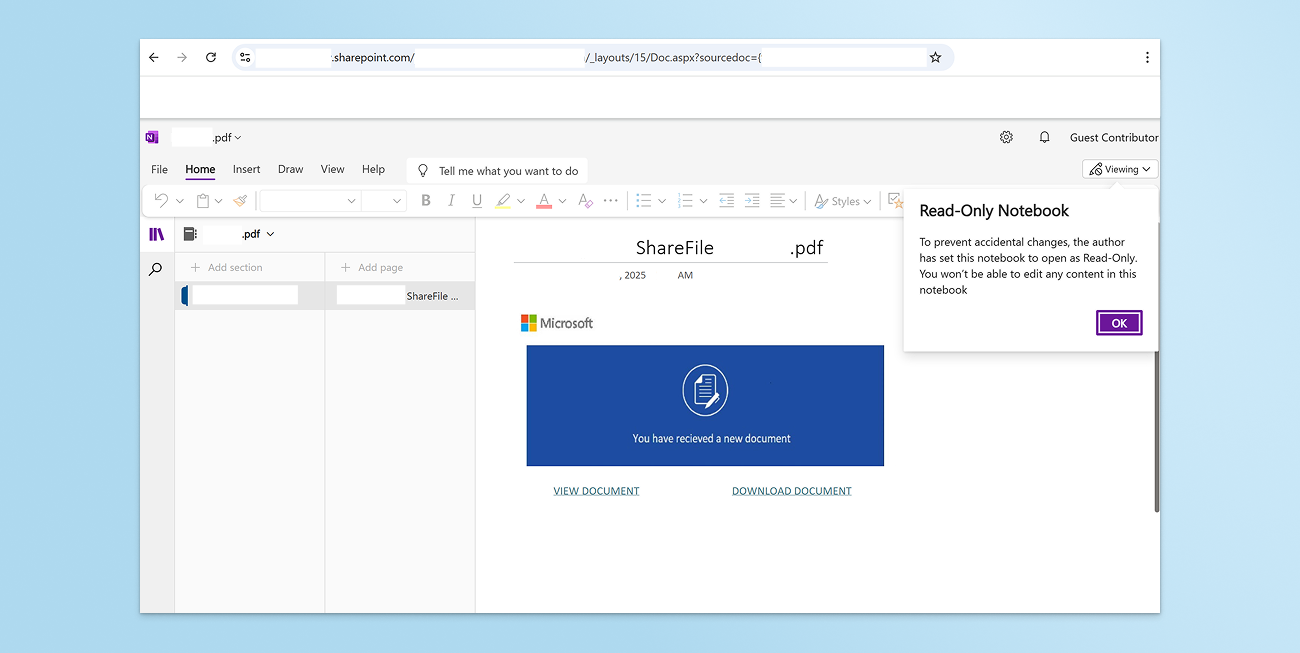
2. Trusted Infrastructure as an Evasion Layer
We increasingly observe attackers leveraging:
- Legitimate cloud platforms, such as attacker-controlled SharePoint instances
- Compromised but reputable websites
- Compromised email addresses
These platforms act as intermediary points between the phishing email and the final malicious page. Using links to trusted sites and mail from reputable domains makes detecting phishing emails much more difficult, allowing the email to bypass security controls and raising the likelihood of a successful attack.
Because the initial domain carries trust and a clean reputation history:
- Phishing emails are more likely to be delivered
- Links appear credible to users and tools alike
- Detection based on domain reputation and sandbox detonation is often evaded
Reputation-based controls are not broken, but they are being intentionally leveraged in attacks.
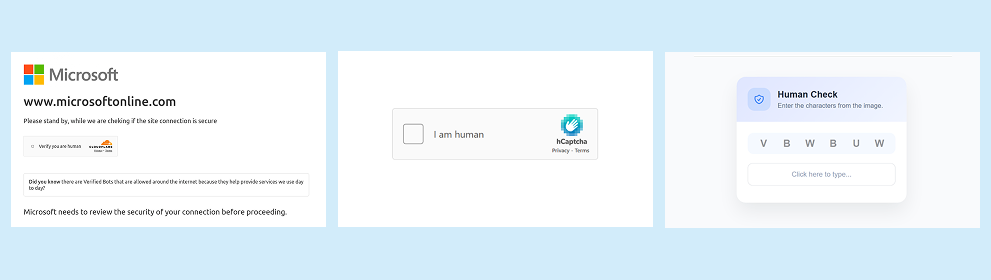
3. Cloaking and Conditional Execution Show Different Content
Many phishing sites now employ conditional logic to determine who sees malicious content. Common triggers include:
- User-Agent inspection
- Referrer check
- URI query parameters
- Email input validation
- The browser is a new visitor to the site
- Geolocation, preferred language, or other browser fingerprinting techniques
This evasive method ensures that unwanted visitors, such as automated tools, are shown blank pages or benign content, enabling the malicious site to maintain a good reputation.
If the visitor appears to be an automated scanner or analyst, the site may:
- Display benign content
- Return a blank page
- Redirect to a trusted site
The result: Only targeted users receive the malicious prompts, malicious infrastructure remains active longer while appearing harmless to scanners and reputation lists, and analysts are left with more questions than answers.
if (VyOrvhfHFD["web" + "driver"] || wYkFRxlrAV["call" + "Phantom"] || wYkFRxlrAV["_phantom"] || VyOrvhfHFD["user" + "Agent"].includes("Burp")) { wYkFRxlrAV["loca" + "tion"] = "about:blank"; }4. OOB Analysis That Sees Something Different
During investigations, we frequently encounter domains and URLs that:
- Redirect analysts to benign sites (e.g., Google, Amazon, or Yahoo)
- Serve clean content during sandbox analysis
- Appear benign when accessed directly
Without in-browser visibility tied to the original browsing session, analysts may never see the malicious content that was actually delivered to the victim.
This crucial question becomes difficult to answer: What did the user actually see and do?

5. CAPTCHA as a Shield Against Automation
CAPTCHAs are increasingly used not just to block bots but to block basic security tooling. By requiring human interaction before revealing content, attackers:
- Prevent automated crawlers from reaching final payloads
- Delay malicious classification
- Extend campaign lifespan
Using CAPTCHAs limits web crawlers and automated security web scanners from correctly seeing and classifying the final domain as malicious, enabling the malicious site to remain active for longer with its reputation in good standing.
The results are delayed classifications, longer-lived phishing infrastructure, and a higher likelihood of successful attacks.
The Larger Pattern: Evasion by Design
The above procedures represent only a fraction of the broader arsenal attackers use to effectively evade traditional security tools, automated web crawlers, and OOB analysis—enabling campaigns to be stealthier, more effective, and longer-lived.
Collectively, our observations of these methods over the preceding year represent something more important: Attacks are now structured specifically to evade analysis that happens outside the intended victim’s browser session.
Email security, SWGs, and reputation engines still serve important roles. But when campaigns depend on user interaction, trusted infrastructure, and conditional execution, large visibility and detection gaps emerge.
Security teams are often left with questions and assumptions rather than answers and truths, creating investigative friction for analysts and risk ambiguity for security leaders.
Where Visibility Must Shift: In-Line, Browser-Native
As browser-based attack chains grow more evasive, detection must move closer to the execution layer.
Security teams increasingly need the ability to:
- Observe full browser interaction sequences
- Identify conditional content delivery
- Understand what users actually experienced
- Tie behavior to outcomes in real time
When attackers design campaigns to defeat traditional controls, automated scanning, and OOB analysis, the most reliable vantage point becomes the browser session itself. Browser-native visibility and real-time context are the leverage points security teams need to efficiently and effectively mitigate and respond to browser-based attacks.
Read about emerging attacks and browser visibility gaps of traditional controls in our State of Browser Security 2026 Report.

.png)

%20copy.jpg)
.png)